What if the high-security credential in your wallet is actually more vulnerable to a sudden technical failure than a security breach? Many professionals in Singapore rely on these systems daily, yet the fear of being locked out or facing high replacement fees from a management office remains a constant concern. You may feel confused by the technical gap between Legacy and SE versions, especially when considering hid iclass card cloning for a backup. It’s a valid worry, as the security landscape has shifted with CISA alerts like CVE-2024-23806 highlighting vulnerabilities in configuration cards as recently as February 2024.
We’ll help you understand these technical complexities and show you how to verify if your specific card can be professionally duplicated. This guide explores why reader firmware, like version 8.6.0.4 or higher, impacts duplication and how to identify your system without the guesswork. You’ll learn the steps to secure a working spare without any technical hassle, ensuring your original access system remains completely undisturbed. Final confirmation of compatibility is always required, but professional verification is the most reliable way to maintain your access security in 2026.
Key Takeaways
- Understand the 13.56 MHz technology powering Singapore’s access systems and why its high-security encryption requires a specialist approach for duplication.
- Learn about the technical complexities involved in hid iclass card cloning, including how Elite Keys and diversified structures maintain system integrity.
- Discover the importance of a professional assessment to prevent card corruption or “bricking,” which can occur during improper duplication attempts.
- Identify the specific card markings and reader details needed for a technical assessment, as final confirmation of service is always subject to system compatibility.
- Find out how to secure a reliable backup card without the need for specialized DIY hardware or the risk of disturbing your existing access settings.
What is HID iClass Technology and How Does It Secure Access?
HID iClass represents a contactless smart card technology designed for advanced security and interoperability. Developed by HID Global, this system operates at the 13.56 MHz frequency, which is a significant step up from older proximity technologies. In Singapore, you’ll find these systems protecting high-end condominiums, government buildings, and corporate offices in the Central Business District. It’s the standard for environments where data integrity is paramount. Unlike basic RFID cards that simply broadcast a number, iClass utilizes mutual authentication and encrypted data transfer. This means the card and reader must perform a digital “handshake” using secret keys before any information is exchanged. Because of these security layers, hid iclass card cloning is a complex task that requires a deep understanding of cryptographic structures.
The Evolution of iClass Security Standards
Security standards have advanced significantly since the technology’s inception. Legacy iClass is the original version, frequently found in residential developments built in the early 2000s. While it was a pioneer, it lacks some of the modern defenses found in iClass SE (Sio-Enabled). The SE version uses a multi-layered security protocol called the Secure Identity Object (SIO). This protocol acts as a secure “wrapper” for data, providing an extra layer of protection independent of the card’s physical chip. There is also iClass SR, which is often tailored for specific industrial applications requiring secure read and write capabilities for inventory or equipment tracking. Each version presents different challenges for duplication, and success often depends on the specific firmware of the reader.
Why iClass Differs from Standard 125kHz RFID
The primary difference lies in the frequency and data capacity. Standard 125kHz proximity cards are relatively simple. They often transmit their ID number in plain text, which makes them susceptible to “sniffing,” where a device nearby captures the signal without physical contact. iClass cards operate at a higher frequency, allowing for complex encryption and larger data storage. Because the encryption is so robust, hid iclass card cloning is not a simple procedure. If you need to duplicate door access cards that use iClass technology, the process involves decrypting these secure layers rather than just copying a simple frequency. It’s a precise operation where errors can lead to the card becoming unusable or “bricked.” This is why a methodical, specialist approach is necessary to ensure the new card works seamlessly with your existing reader. Final confirmation of compatibility is always required before any service can proceed.
The Complexity of HID iClass Card Duplication
Duplicating high-security credentials isn’t as simple as copying a barcode or a standard magnetic stripe. HID iClass systems use a sophisticated cryptographic framework that provides layers of protection. One of the most significant hurdles is the “Elite Key” program. This system uses unique, customer-specific authentication keys rather than standard industry keys. If your facility uses an Elite Key, standard duplication methods won’t work. Because these keys are diversified, meaning they can change per card or per facility, hid iclass card cloning requires specialized knowledge and professional-grade hardware. Attempting to bypass these protections with unverified tools can lead to “bricking” your original card. This results in the card becoming permanently unresponsive to any reader, leaving you without access entirely.
Security risks are a serious consideration in this field. A CISA vulnerability report released in February 2024 highlighted specific flaws in reader configuration cards that could expose sensitive data. This underscores why professional verification is essential before attempting any card service. Compatibility is never assumed. It varies significantly depending on your specific reader configuration, firmware version, and the card’s encryption level. What works for a legacy system may fail completely on a modern SE installation. Final confirmation of compatibility is always required before any service can proceed.
Understanding Encryption Keys and Data Blocks
Master keys and application keys work together within the iClass ecosystem to secure specific data blocks. While some basic devices can read the Card Serial Number (CSN), this is often insufficient for access in modern Singaporean offices or condos. Secure data areas are protected by mutual authentication. Professional hardware is necessary to interface with these encrypted blocks without triggering security lockouts. If you’re unsure about your card’s type, you can verify your access card compatibility with an experienced specialist to avoid unnecessary risks.
Common Challenges in the Duplication Process
High-security credentials often have “Read-Only” restrictions. These prevent unauthorized hardware from even seeing the internal data structure. Another challenge involves managing the response timing. Modern readers are programmed to detect the slight delay caused by low-quality cloned chips. If the new credential doesn’t mimic the original card’s timing perfectly, the system will reject it as a security threat. This is why simple “cloners” found on budget retail sites are typically ineffective for iClass systems. They simply don’t have the processing power to handle the required cryptographic handshakes or the precision needed for diversified keys. Ensuring the new credential works seamlessly requires a methodical approach that prioritizes system stability.

Verifying Compatibility for Your Access System
Determining if your specific credential supports hid iclass card cloning requires more than a simple visual inspection. While many users in Singapore attempt to identify their cards via online forums or photos, these methods are often inaccurate. The external shell of an access card doesn’t always reflect the internal chip’s security protocol or the specific encryption used by your building’s management. A technical assessment is essential because a card’s ability to be duplicated depends on the specific reader configuration and firmware version. To begin an assessment, you’ll generally need to provide the card markings, the reader model installed at your facility, and occasionally the facility code. Visiting a specialist workshop remains the most accurate method because it allows for a physical diagnostic test that a photo simply cannot provide. Final confirmation is always required as results vary significantly by system.
Step 1: Identifying Your Card Model
Start by looking for markings such as ‘iClass’, ‘iClass SE’, or ‘iClass DP’ on the back of the credential. Many Singaporean condominiums and corporate offices use the 200x or 210x series numbers, which are key indicators of the hardware generation. It’s common to encounter unbranded cards in local residential developments, but these may still belong to the iClass family and operate at the 13.56 MHz frequency. Because internal chips vary even within the same branded shell, visual identification is only a preliminary step. If you’re unsure about your card’s type, getting a professional to duplicate door access cards starts with this critical identification phase.
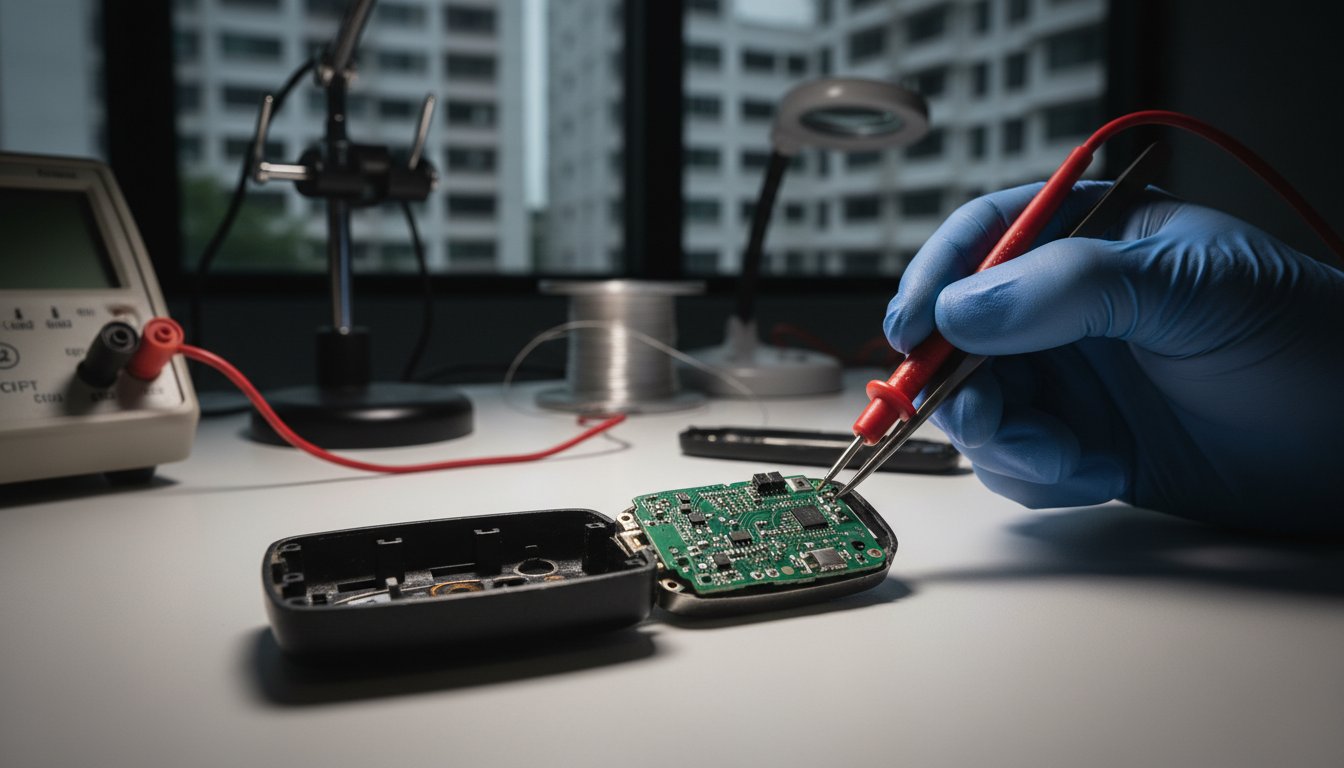
Step 2: Professional Verification Methods
Specialists use precise diagnostic tools to read the card’s specific protocol and frequency. This step determines if the card is a ‘Legacy’ version or if it utilizes ‘High Security’ encryption like the SIO-Enabled (SE) models. The feasibility of duplication depends on the current system version and whether features like the ‘Elite Key’ are active. Since technology varies across different developments, final confirmation is always required at the point of service. This ensures the new credential will function correctly with your specific reader without any technical hassle. Professional verification prioritizes accuracy, ensuring that any attempt at hid iclass card cloning is based on verified data rather than assumptions. If you need a reliable assessment of your access card, contact a specialist at Soxxi Master for an accurate confirmation of your specific needs.
Why Professional Duplication is Preferable to DIY Methods
While online communities often discuss using portable devices like the Proxmark3 or Flipper Zero, the reality of hid iclass card cloning is far more demanding than a simple click of a button. These tools are not only expensive, with professional-grade versions like the Proxmark3 X retailing for approximately $79.99 in early 2026, but they also require significant technical proficiency. Using them without proper training often leads to unintended consequences. A professional service provides a reliable outcome while ensuring your original access credential remains completely undisturbed and functional. You avoid the hidden costs of purchasing specialized hardware that you might only use once.
The Risks of Using Unverified DIY Tools
DIY enthusiasts often underestimate the complexity of encrypted systems. Incorrectly formatted data packets can trigger security alarms or reader lockouts, alerting building management to unauthorized access attempts. There’s also a significant risk of data corruption. A single error during the writing process can render your only working card useless, forcing you to pay for an expensive replacement from the management office. In the context of Singapore’s strict regulatory environment, the use of specialized tools to bypass security protocols can also raise legal concerns. It’s better to rely on a transparent, professional process than to risk your access privileges with unverified hardware. Professional verification ensures that hid iclass card cloning is done safely without compromising the system’s integrity.
The Value of Specialist Expertise
Specialists utilize commercial-grade equipment that offers higher precision than consumer-level devices. This hardware allows for a deeper analysis of the card’s data structure without the risk of corruption. Engaging a Professional Key Duplication Service ensures that the new credential is an accurate match for your specific reader. With over 18 years of experience in Singapore’s access control market, we understand the nuances of local condominium and office systems. This expertise allows us to determine compatibility quickly and efficiently, saving you the time and frustration of trial and error. You don’t have to worry about the steep learning curve or technical errors associated with DIY methods. It’s a straightforward process that prioritizes your peace of mind and system security.
If you’re looking for a hassle-free way to secure a spare card, get your access card verified by a specialist today to ensure a seamless and accurate result.
Specialist Access Card Services at Soxxi Master
Soxxi Master has served as a pioneer in Singapore’s key and access card industry for over 18 years. We’ve seen the evolution of security from simple proximity cards to the advanced 13.56 MHz systems protecting modern developments. Our long history allows us to handle complex requests with a methodical approach to duplicate door access cards with precision. We understand that residents and corporate clients need a reliable backup without the risk of system failure. That’s why our commitment to verification is absolute. We don’t assume compatibility; we verify it through a rigorous assessment of your card’s specific details. Our workshop is equipped with commercial-grade technology that handles the intricate cryptographic handshakes required for modern credentials.
This setup is part of our identity as “the master of key,” providing a complete solution for all things key, whether mechanical or electronic. We’ve helped thousands of clients across Singapore secure their premises and maintain access continuity. Whether you’re a property manager overseeing a large facility or a resident needing a spare for a family member, our service remains efficient and professional. Every request is handled with the same level of expert care to ensure your original system remains undisturbed. Final confirmation is always required before we proceed with any duplication service.
Our Verification-First Approach
We prioritize the security and functionality of your existing access system above all else. Before any attempt at hid iclass card cloning, our experts perform an assessment to determine if your specific model is a candidate for duplication. This involves checking the hardware generation and firmware compatibility. We provide clear communication regarding what is possible for your specific system. If a system is locked by an Elite Key or a high-security protocol that prevents duplication, we’ll inform you upfront. This transparent process ensures you don’t waste time or risk damaging your original credential. It’s a hassle-free experience that puts your needs first.
How to Get Started with Your Request
Getting started is a straightforward, three-step process designed for your convenience. First, you can contact us via WhatsApp with a clear photo of the front and back of your card. This allows for an initial assessment based on card markings and series numbers. For a definitive answer, we recommend a visit to our workshop at 37 Jalan Pemimpin. Physical verification using our diagnostic tools is the only way to ensure accuracy. Our team is ready to guide you through the technical requirements to get a working spare card without any technical hassle. Contact Soxxi Master for an accurate assessment of your access card needs and let our specialists provide the confirmation you require.
Secure Your Access with Professional Verification
Navigating the complexities of high-security encryption requires more than just the right tools; it demands a deep understanding of how reader firmware and diversified keys interact. As we’ve explored, the risks associated with unverified hid iclass card cloning attempts are significant, ranging from card corruption to permanent reader lockouts. It’s essential to rely on professional expertise to ensure your original credentials remain safe while you secure a reliable backup for your daily needs.
With over 18 years of experience as a pioneer in Singapore’s key industry, Soxxi Master provides the technical accuracy required for both mechanical and electronic access systems. Our methodical approach prioritizes your security, offering a seamless experience from initial assessment to final confirmation. Visit our workshop at 37 Jalan Pemimpin for a physical verification of your card’s compatibility. Our specialists are ready to help you navigate these advanced systems without the technical hassle or uncertainty of DIY methods.
Contact Soxxi Master for a Professional Access Card Assessment today to confirm your specific requirements and ensure your access remains uninterrupted.
Frequently Asked Questions
Is it possible to clone an HID iClass SE card?
Cloning an HID iClass SE card is possible depending on the specific encryption level and reader firmware. These cards use a Secure Identity Object (SIO) that provides multi-layered protection. Because security varies by system, a professional assessment is necessary to determine compatibility. Final confirmation is always required at the point of service to ensure the new credential functions seamlessly with your building’s reader without any technical hassle.
Will duplicating my access card affect the original one?
Professional duplication does not affect your original access card. Our specialists use non-destructive methods to read the data blocks without modifying the original chip’s settings. It’s safe and ensures your existing card remains fully functional. You should avoid DIY methods using unverified hardware; these carry a high risk of corrupting the data or bricking the card, which would require an official replacement from management.
How long does it take to duplicate an iClass card?
The duplication process usually takes between 15 to 30 minutes once we verify compatibility. This timeframe allows our specialists to perform the necessary cryptographic handshakes and ensure data accuracy. While most cards are processed quickly, some high-security systems may require a few extra minutes for complete verification. We aim for an efficient and accurate service so you can get back to your routine without delay.
What should I do if my iClass card is not supported for cloning?
If your card is not supported due to restricted protocols like the Elite Key program, we recommend contacting your building management. We prioritize the security of your access system and won’t proceed if the duplication risks system instability. Our experts will provide a clear explanation if your model isn’t a candidate for service. This transparent approach ensures you have the correct information to resolve your access needs officially.
Is it legal to have a spare copy of my condo access card in Singapore?
It is generally acceptable for residents to have a spare copy for personal convenience, but you should review your tenancy agreement or MCST bylaws. Many clients choose professional duplication to avoid the high administrative fees charged by management offices. Our services are designed for legitimate users who need a working backup. We encourage all clients to ensure their requests align with their specific building’s access policies.
Can you duplicate HID iClass cards if all keys are lost?
We cannot perform hid iclass card cloning if all original cards are lost. Our duplication process requires a working source card to read the encrypted data and authentication keys. If you don’t have a functional card, your only option is to request a new one from your building’s administrator. Once you have a replacement, we can then assist you in creating a backup to prevent future lockouts.
What is the difference between HID Prox and HID iClass?
HID Prox is an older technology operating at 125kHz without data encryption, making it easier to duplicate. In contrast, HID iClass operates at 13.56MHz and uses mutual authentication to secure data. This higher frequency allows for complex encryption that protects against unauthorized signal sniffing. Because iClass is more advanced, it requires commercial-grade equipment and specialist expertise to ensure a successful and accurate duplication result.
Do I need to bring my card to the shop for verification?
Physical verification is essential for an accurate assessment of your system. While you can send a photo via WhatsApp for initial identification, our diagnostic tools must read the internal chip to confirm compatibility. Visiting our workshop at 37 Jalan Pemimpin allows us to test the card’s protocol and frequency directly. This ensures that any attempt at hid iclass card cloning is based on verified technical data rather than visual assumptions.