On May 12, 2026, a project manager at the International Business Park discovered the hard way that a basic clone doesn’t always open the door, leaving them stranded outside a high-stakes meeting. Many professionals seeking office access card duplication jurong east face the same anxiety; the fear that a spare card might be rejected by sophisticated office readers. It’s a valid concern, as modern systems like HID iClass or Mifare Desfire use complex encryption and two-way authentication that requires specialist verification rather than just a simple copy to function correctly.
We understand that your workday is already packed and you don’t have time for multiple trips or failed attempts at the security gate. This guide clarifies the technical requirements for duplicating high-security cards and explains why professional verification is essential for a working spare. You’ll gain a clear understanding of your specific RFID technology and learn how to obtain a functional duplicate, subject to system compatibility, with minimal disruption to your schedule. Final confirmation of compatibility is always required before any service can proceed to ensure the reliability you expect.
Key Takeaways
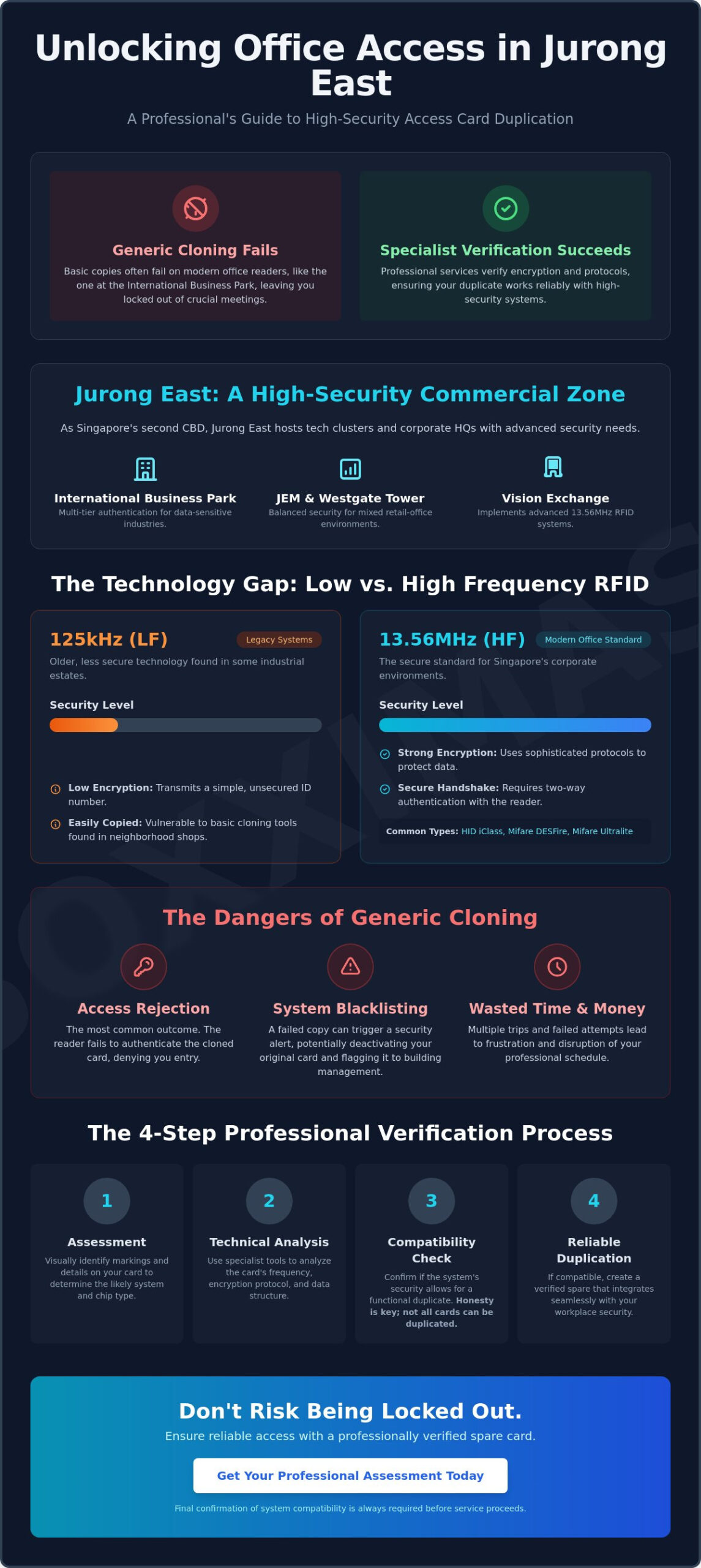
- Understand the evolving security landscape in Jurong East commercial hubs, including the International Business Park and Westgate Tower, where high-security protocols are standard.
- Learn why professional office access card duplication jurong east is necessary to navigate the complexities of 13.56MHz high-frequency encryption and modern RFID systems.
- Discover how specialist verification helps prevent common risks like reader rejection or system blacklisting, which are frequent issues with unverified generic cloning.
- Identify the markings and details needed to prepare for a duplication service, including how visual verification helps determine initial system compatibility.
- Find out why a professional assessment is essential to ensure your spare access card functions reliably, subject to specific building system requirements.
Navigating Office Access Card Duplication in Jurong East
Office access card duplication involves creating a functional secondary credential specifically designed for corporate environments. In Jurong East, this process is influenced by a diverse commercial landscape that has evolved rapidly since the 2008 Master Plan designated the area as Singapore’s second Central Business District. Areas like the International Business Park (IBP) host specialized tech clusters and headquarters that require robust security. Unlike residential condominiums, office systems in this region often utilize Proximity Card Technology with higher encryption levels to protect sensitive corporate assets. Finding a specialist for office access card duplication jurong east is vital because these systems demand an understanding of Singaporean corporate infrastructure and the specific hardware deployed across different business hubs.
Major Commercial Hubs in Jurong East and Their Security
The security standards at International Business Park (IBP) often involve multi-tier authentication, especially in buildings that house data-sensitive industries. Retail-office hybrids like JEM and Westgate Tower house professional suites that balance high foot traffic with restricted access protocols. Modern office towers, such as Vision Exchange, frequently implement advanced RFID requirements like 13.56MHz high-frequency systems. These environments prioritize data integrity, meaning a simple clone might not bypass the reader’s verification handshake. It’s common for these systems to be updated periodically, so a duplicate that worked in 2023 might require a different technical approach in 2026. Proximity to these hubs allows a specialist to stay updated on the specific reader brands commonly used in the district.
Why a Specialist is Required for Office Credentials
A common mistake is assuming that any neighborhood kiosk can handle corporate-grade RFID. There is a significant difference between simple frequency copying and technical protocol verification. Neighborhood key-cutting shops often use generic tools that copy the raw frequency but fail to replicate the encrypted handshake required by high-security readers. These “one-size-fits-all” tools often result in cards that the reader rejects or, in some cases, triggers a system alert. A professional service provider evaluates the card’s specific technology before proceeding. You can learn more about our process for a duplicate door access card to see how verification ensures a reliable result. Compatibility is never assumed; it’s verified based on the card type and the specific system requirements of your office building. Final confirmation is always required before any service proceeds to ensure the spare card integrates seamlessly with your workplace security.
Understanding High-Security Office RFID Systems
Modern Singaporean office buildings have largely moved away from the basic proximity cards of the past. Today, the majority of corporate environments utilize 13.56MHz High Frequency (HF) systems. These systems are significantly more secure than the legacy 125kHz Low Frequency (LF) systems still occasionally found in older industrial estates around Jurong. The primary difference lies in how data is stored and transmitted. While LF cards often transmit a simple ID number, HF cards use sophisticated encryption to secure data within the chip. This makes office access card duplication jurong east a technical task that requires specific hardware and expertise rather than a simple cloning tool. Compatibility is never assumed; every card must be assessed individually because even cards that look identical may house different internal chips. A physical assessment allows us to determine the exact technical requirements for your specific building.
Common Office Card Technologies
Corporate security in Singapore is dominated by a few key players. HID iClass and HID Proximity remain industry standards, offering varying levels of encryption and read ranges. In newer Jurong East towers, you’ll often encounter Mifare DESFire or Mifare Ultralite systems. These protocols are designed with high-security handshakes that prevent unauthorized access. Some modern offices are also shifting toward proprietary encrypted fobs or even mobile credentials that reside on a smartphone. Because these technologies vary widely, a specialist must verify the exact version of the chip to determine if a functional duplicate is possible. For those using combined office and vehicle access, our key duplication services often involve assessing whether the RFID element can be integrated into a single credential, subject to system compatibility.
The Verification Process for Encrypted Cards
Identifying the specific protocol used by your office building is the first step in a successful duplication. Specialists use diagnostic tools to read the card’s frequency and identify any “anti-copy” features. These features are designed to block generic duplicators and can cause a reader to blacklist a card if an incorrect copy is attempted. If your office card is integrated with car park access, we may request specific vehicle details, such as a chassis number, to ensure the duplicated credential communicates correctly with the gantry system. This level of verification is essential for office access card duplication jurong east where readers are often programmed with strict security rules. For a professional assessment of your current credential, you may consult our technical team. Final confirmation is always required before we proceed with any service, as success depends entirely on the specific system compatibility of your building.
The Risks of Generic Cloning vs. Specialist Verification
Choosing a service for office access card duplication jurong east requires more than just finding a nearby vendor. While basic kiosks may offer a quick copy, the technical risks of substandard cloning are significant in a corporate setting. Many professional duplication services in Singapore maintain a success rate of 90% to 99% for compatible cards, but this high rate is only achievable through precise technical matching. Modern office readers are programmed with security logic that can detect clones that don’t perfectly replicate the original chip’s signature. If a reader identifies a credential that doesn’t match the expected technical handshake, it may reject the card or, in some instances, blacklist the original card from the system entirely. This leads to an inconvenient situation at the security gantry that requires intervention from building management.
Avoiding Substandard Duplication
The quality of the blank chip used in the duplication process is a critical factor for long-term reliability. Substandard chips often fail within 30 days of consistent use due to antenna degradation or memory corruption. There’s also a physical risk to your original credential; unverified cloning devices can sometimes corrupt the data on the source card during the reading process. Using professional-grade hardware ensures that the data is read accurately without compromising the integrity of your primary card. This technical precision is why we emphasize that compatibility is not assumed and must be verified by a specialist before any work begins. It’s a conservative approach that prioritizes the safety of your existing credentials over a quick, unverified fix.
Professional Standards and Confidentiality
Corporate security protocols demand a level of discretion that goes beyond simple key cutting. We prioritize technical accuracy over marketing hyperbole, which is why you won’t see us using terms like “guaranteed” or “unblockable.” These claims are often misleading because success depends entirely on the specific encryption level of the building’s system. Our specialist promise involves a conservative assessment of your card’s technology. Some vendors in Singapore are registered with the Singapore Police Force (SPF) as security system providers, reflecting the serious nature of handling office credentials. If a system uses high-level encryption that cannot be safely duplicated, we’ll inform you upfront rather than providing a faulty product. This methodical approach is part of our commitment to being a trusted specialist for corporate clients. We focus on providing a reliable spare that integrates with your workday without the fear of sudden failure or security alerts. Final confirmation of compatibility is always required before any service proceeds to ensure the result meets our professional standards.
How to Prepare for Your Access Card Duplication
Preparation is the first step toward a hassle-free experience. Before you arrange for office access card duplication jurong east, taking a moment to gather specific details ensures our technical team can provide a more accurate assessment. It’s not just about the physical card; it’s about understanding the security layer it carries. We recommend starting with a visual check. Look for any embossed brand names or serial numbers on the card’s surface. These markings are often the first indicator of whether your system uses legacy technology or modern encryption protocols.
A clear photo of your card, shared via WhatsApp, allows us to perform a preliminary verification. This digital step is a core part of our process, designed to save you an unnecessary trip if a system is proprietary or non-duplicable. When scheduling your visit, balancing your workday convenience with the need for technical precision is essential. While the fabrication itself is efficient, a specialist needs time to verify the protocol and ensure the data write is accurate. Always bring your original card, any fobs, and if your access includes a car park gantry, have your vehicle’s chassis number ready for verification.
Step-by-Step Assessment Guide
- Step 1: Inspect the card. Check for brand names like HID, Indala, or AWID. Even faint markings help us identify the specific technology used in your building.
- Step 2: Note multi-purpose usage. Does your card handle lift access, office entry, and car park gantry? Integrated systems often require specific fabrication methods to ensure all functions work.
- Step 3: Contact a specialist. Share your findings and a photo for a preliminary compatibility check. This ensures we have the correct high-quality blanks ready for your visit.
What to Expect During the Service
The service begins with a technical readout using professional-grade diagnostic tools. This isn’t a simple frequency copy; it’s a verification of the card’s encrypted handshake. Once the protocol is confirmed, the fabrication process uses precision equipment to create a reliable duplicate. We prioritize accuracy over speed because a rushed clone often leads to reader rejection. After the duplicate is created, final confirmation is always required. We encourage you to test the new credential at your office building’s reader as soon as possible. For a seamless start to the process, you can reach out to our technical team for an initial evaluation. Final confirmation of compatibility for office access card duplication jurong east is always subject to the specific building system and reader requirements.
Soxxi Master: Professional Access Solutions for Singapore
Soxxi Master stands as a pioneer in Singapore’s electronic access industry, having established a reputation for technical precision over 18 years of experience. We provide a comprehensive range of solutions, from high-security RFID access cards to precision-engineered auto gate remotes. Our approach is methodical; we don’t just copy credentials. We verify the underlying technology to ensure every spare we produce functions reliably with your specific hardware. Businesses across the island, including those in the rapidly growing commercial hubs of the west, look to us for office access card duplication jurong east because we prioritize technical integrity over simple cloning. Our commitment to accuracy ensures that the solutions we provide integrate seamlessly with your existing security infrastructure.
The Specialist Advantage
Our expertise is built on nearly two decades of handling complex automotive and electronic access systems. This experience allows us to maintain a holistic understanding of security, often referred to as being “the master of key.” While many shops focus only on mechanical keys, our primary hub at 37 Jalan Pemimpin is equipped with specialized diagnostic tools for complex technical duplications. This facility allows us to assess high-encryption protocols that standard kiosks cannot handle. Whether you’re dealing with a legacy 125kHz system or a modern encrypted 13.56MHz chip, our assessment process is conservative and focused on long-term results. We understand that a failed card isn’t just an inconvenience; it’s a disruption to your professional day. By focusing on “all things key,” we provide a reliable point of contact for all your access requirements.
Securing Your Office Access
Obtaining a functional spare starts with an accurate assessment of your specific card model. Because office security systems vary by building management and system age, final confirmation of compatibility is essential before any service proceeds. We avoid marketing hyperbole and instead offer realistic, technical evaluations based on the specific chip and reader requirements of your workplace. Beyond the initial duplication, we provide professional after-care and technical support to ensure your credentials continue to perform as expected. If you require a reliable spare, we encourage you to contact us for a professional assessment of your office access needs. You can reach our team through our online form to begin the verification process. Every service we provide for office access card duplication jurong east is subject to system compatibility, ensuring that your security remains intact and your access stays seamless.
Secure Your Professional Access with Specialist Verification
Obtaining a reliable spare card shouldn’t be a source of stress or workday disruption. By prioritizing a verification-first approach, you avoid the common pitfalls of reader rejection and system blacklisting that often follow generic cloning attempts. With 18 years of specialist experience in Singapore, Soxxi Master focuses on the technical handshakes required for HID, iClass, and encrypted Mifare systems. This expertise ensures that your access stays seamless across the complex security environments of the west.
When you seek office access card duplication jurong east, choosing an expert who understands the specific commercial infrastructure of the district is the most efficient path to a functional spare. Our methodical process respects corporate security protocols while delivering the technical accuracy you need for high-security environments. Final confirmation is always required before we proceed, as success depends on your building’s specific system compatibility. Ready to get started? You can contact Soxxi Master for a professional access card assessment to confirm your specific needs. We’re here to help you secure the right solution for your office credentials.
Frequently Asked Questions
Can all office access cards in Jurong East be duplicated?
Not every credential is compatible with duplication. Success rates for office access card duplication jurong east often reach 90% to 99% for standard RFID types, but highly encrypted systems vary. Specialist verification is essential to determine if your specific building’s security protocol allows for a functional secondary card. We assess each chip individually because even cards that look identical can house different internal technologies.
Is it safe to clone an encrypted HID iClass card?
Cloning is safe when performed with professional-grade diagnostic tools that respect the card’s data integrity. We use a verification-first approach to ensure the handshake is replicated accurately. Success is always subject to the specific encryption version used by your office building and the reader’s security settings. This methodical process helps prevent common issues like reader rejection or original card corruption.
How long does the duplication process typically take for an office card?
Duplication usually takes 15 to 30 minutes once the protocol is verified. This includes the technical readout and chip fabrication. Market data from May 2026 shows that standard RFID duplication often falls within the S$8 to S$15 range, while high-security HID iClass cards can range from S$40 to S$80 across Singapore. We prioritize technical accuracy to ensure the spare works on your first attempt.
Will my office security system know if I am using a duplicated card?
Advanced readers can identify clones that fail to replicate the full encrypted protocol. If a clone is detected, the system might reject the entry or log a security alert. Our specialist fabrication aims for a precise match to avoid these risks, though final results depend on specific system compatibility. Professional verification ensures your duplicate mimics the original credential’s behavior to the reader.
What should I do if my duplicated card stops working after a system update?
If a card fails after an update, the reader’s encryption keys or security logic likely changed. You should return to your specialist for a technical readout. We can then assess if the updated system requirements can be met with new fabrication methods, as compatibility varies by reader version. Systems in high-security towers are updated more frequently than those in older industrial estates.
Do I need to provide my office building management’s permission for a spare card?
We duplicate cards provided you have the original credential in your possession. You’re responsible for following your office’s security policies or MCST by-laws regarding spare cards. Our role is to provide a technically accurate duplicate for your convenience, subject to the technical limits of the system. We recommend checking your building’s regulations before proceeding with any duplication service.
Can you duplicate cards that also have integrated car park access?
Integrated credentials can often be duplicated if the RFID technology matches our supported protocols. For office access card duplication jurong east involving parking gantries, we verify compatibility using your card and vehicle details. This ensures the spare card triggers the gantry reader as reliably as your original. Final confirmation is always required before we proceed to ensure the integrated functions work seamlessly.
What is the difference between a card and an RFID key fob for office use?
The difference is purely physical, as both house an internal chip and antenna. In many cases, we can duplicate a card’s data onto a more convenient key fob or vice versa. This flexibility depends on the compatibility of the specific RFID chip with our available blanks. While cards fit in wallets, fobs are often preferred for their durability and ease of attachment to keyrings.




